Have you ever opened your inbox and noticed emails that look suspicious, push you to act quickly, or ask for sensitive information? Scam emails have become more sophisticated than ever. In 2026, cybercriminals use advanced techniques such as AI-generated messages, impersonation of trusted companies, and social engineering tactics designed to trick even cautious users.
These messages often pretend to be from banks, delivery companies, government agencies, or popular online services. Their goal is simple: make you click a malicious link, download an infected attachment, or reveal personal information like passwords or credit card details.
The good news is that stopping scam emails is possible. By combining smarter email filters, proper reporting practices, and a few simple safety checks, you can significantly reduce the chances of falling victim to these attacks.
In this guide, you’ll learn how scam emails work, how modern email filters detect them, how to report suspicious messages, and the practical steps you can take to keep your inbox secure.
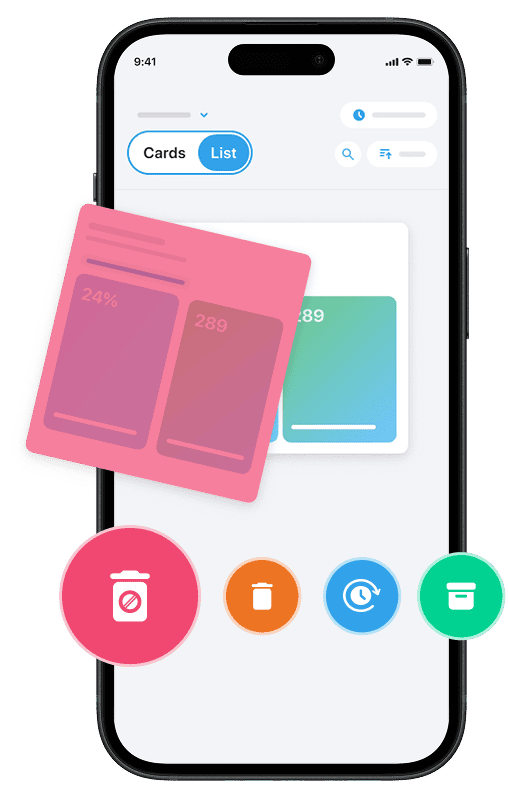
And if you want to stop scam emails for good, just install our Cleanfox app — it helps remove spam and unwanted emails from your inbox with just one click.
Advanced Filtering Techniques
Say goodbye to spam, clutter, and chaos.
Our smart email cleaner filters out junk, organizes your inbox, and helps you focus on what really matters.
✅ Block spam automatically
✅ Organize emails by priority
✅ Keep your inbox clean
✅ Clean old emails you don’t read
📱 Available on the App Store and Google Play.
Understanding Modern Email Filters
Imagine your inbox as a fortress gate—modern email filters in 2026 act as smart guards. They don’t just check IDs; they analyze behavior, patterns, and signals that may indicate malicious intent behind every message. Platforms like Microsoft Exchange Online Protection (EOP) and Gmail deploy layered defenses: connection filtering blocks suspicious senders, while AI-powered machine learning scans content, attachments, and sender reputation. This helps detect advanced threats like phishing, which older keyword-based systems might miss.
In recent years, AI and large language models have improved how providers detect suspicious language patterns and social engineering tactics, such as the fake urgency often seen in Business Email Compromise (BEC) attacks.
However, attackers now also use AI-generated text and compromised accounts, which means filters are not perfect. Some filtering systems also adapt to user signals—such as what you mark as spam or ignore—to improve protection over time.
Setting Up Effective Email Rules
Take control by customizing email rules. In Outlook or Gmail, create filters to route suspicious emails directly to junk.
If you manage a business domain or email infrastructure, start with authentication basics by configuring SPF, DKIM, and DMARC policies to verify senders and reduce spoofing attempts.
In Microsoft 365 environments (for administrators), features such as Safe/Blocked Sender lists and Zero-Hour Auto Purge (ZAP) can automatically remove malicious emails even after they reach a user’s inbox.
Gmail users can also set custom filters for suspicious subject lines or unknown domains and enable built-in phishing detection that adapts based on user behavior and threat intelligence.
Regular audits of these settings ensure they remain effective as threats and filtering technologies continue to evolve.
Third-Party Tools and Extensions
For enhanced protection, organizations may consider third-party security tools such as secure email gateways, DMARC monitoring platforms, or phishing simulation services.
These solutions integrate with platforms like Microsoft 365 and Google Workspace to analyze email patterns, scan links, monitor domain spoofing attempts, and detect compromised accounts. Some tools also enforce strict DMARC policies or run simulated phishing campaigns to strengthen employee awareness.
When combined with native filtering systems, these additional layers help create a more resilient email security setup against modern phishing and scam campaigns.
Reporting and Legal Measures
The Importance of Reporting Scam Emails
When you report a suspicious email, you’re not just protecting yourself—you’re contributing to a broader security ecosystem. Phishing reports help security teams, email providers, and law enforcement track attack patterns and identify coordinated campaigns.
Organizations like the Anti-Phishing Working Group (APWG) rely on reports from users and companies to detect emerging threats and share intelligence across the cybersecurity community.
Without user reports, scammers can operate longer without detection. With consistent reporting, suspicious domains, phishing campaigns, and fraudulent infrastructure can be identified and disrupted more quickly.
How to Report Scam Emails in 2026
You have several options to report spam and phishing depending on your email platform.
Start with your email provider:
In Gmail, open the suspicious email, click the three-dot menu, and select “Report phishing.” This helps Google improve spam detection and block similar attacks.
In Outlook, select the message and use Report > Report phishing or move the message to the junk folder.
You can also forward phishing emails to the Anti-Phishing Working Group at:
[email protected]
For cyber-enabled crimes such as identity theft, online fraud, or email compromise, complaints can also be submitted to the Internet Crime Complaint Center (IC3) at:
For international scams, users may also report incidents through:
When reporting a scam email, include details such as the sender address, date and time received, suspicious links or attachments, and a short description of the situation.
Legal Recourse for Victims
If you’ve fallen victim to a scam email, timing is critical. Contact your bank or credit card provider immediately to report fraudulent activity and freeze compromised accounts.
You should also report the incident to your local consumer protection agency or cybercrime authority. These reports help investigators detect patterns and may support future enforcement actions.
For workplace-related phishing incidents, notify your organization’s security or IT team immediately so they can secure accounts, reset credentials, and investigate potential exposure.
In serious cases involving financial loss or organized fraud, local law enforcement or national cybercrime units may open an investigation.
Document everything: keep email headers, screenshots, message content, and any communication with financial institutions. This information may be important for recovery efforts or legal proceedings.
Proactive Safety Checks and Practices
Regularly Updating Your Security Practices
Staying ahead of security threats requires regular updates and maintenance.
Enable Multi-Factor Authentication (MFA) on all email accounts, ideally using authenticator apps or hardware security keys rather than SMS codes. MFA significantly reduces the risk of account takeover attacks.
Create strong, unique passwords for each account and avoid reusing credentials across services.
Keep operating systems, browsers, and email applications updated to patch security vulnerabilities.
Monitor login activity for unusual behavior such as unknown devices or unexpected geographic locations.
Organizations may also implement outbound filtering, access restrictions, and regular configuration reviews to strengthen overall email security.
Reviewing these practices periodically helps maintain a resilient defense against evolving phishing and scam tactics.
Education and Awareness Training
Technology alone cannot stop every attack—human awareness plays a crucial role.
Train yourself and your team to recognize social engineering tactics used in phishing emails. Always verify unusual requests, especially those involving financial transactions, sensitive data, or urgent actions.
Develop habits such as:
- Double-checking sender email addresses
- Hovering over links before clicking
- Avoiding unexpected attachments
- Confirming suspicious requests through a trusted communication channel
Regular awareness training and phishing simulations help turn security knowledge into instinctive behavior.
Creating a Safe Digital Environment
A secure digital environment relies on multiple layers of protection.
Sensitive communications can be protected using encryption technologies such as PGP, S/MIME, or secure TLS connections, depending on the platform being used.
Avoid connecting automatically to unknown Wi-Fi networks and verify the legitimacy of public hotspots before logging into email accounts.
Use secure websites (HTTPS), enable anti-malware protection, and review privacy settings on social media to reduce exposure to social engineering attacks.
Organizations may also deploy data loss prevention tools, email security gateways, and centralized monitoring systems to strengthen protection.
Combined with reliable backups and recovery plans, these measures help ensure your digital environment remains secure.
Conclusion
Dear reader, you now have the blueprint to take back control of your inbox in 2026.
By combining modern filtering tools, effective reporting, and proactive security habits, you can significantly reduce your exposure to scam emails.
Always verify before clicking links, create strong passwords, enable Multi-Factor Authentication, and keep your devices and software updated.
Security is not a one-time task—it is an ongoing habit. Taking small preventive steps today can protect your accounts, financial information, and peace of mind in the future.
FAQ
What are the most common phishing red flags to watch for in scam emails, like suspicious sender addresses or urgent requests for sensitive information?
Common phishing red flags include:
- Suspicious sender addresses (for example, paypa1.com instead of paypal.com)
- Urgent or threatening language
- Generic greetings such as “Dear Customer”
- Mismatched or shortened links
- Poor grammar or unusual wording
- Requests for sensitive information
- Unexpected attachments
How can I set up email filters effectively to block scam emails in 2026, including handling new threats like QR code phishing?
To block scam emails effectively:
- Use built-in email filtering tools in Gmail, Outlook, or your provider
- Configure SPF, DKIM, and DMARC if you manage a domain or business email system
- Enable phishing detection and spam filtering features
- Create custom filtering rules for suspicious senders or domains
- Enable MFA to protect accounts even if credentials are stolen
- Stay informed about emerging threats such as QR-code phishing
What is the best way to report scam emails to authorities or email providers for maximum impact?
To report scam emails effectively:
Use your email provider’s reporting tools, such as Gmail’s “Report phishing” or Outlook’s reporting options.
You can also forward phishing emails to:
For national cybercrime reporting, contact your country’s official cybercrime or consumer protection agency.
Combining provider reporting with official reports helps security teams detect and disrupt phishing campaigns faster.
Which safety checks should I perform before clicking anything in a suspicious email?
Before interacting with a suspicious email:
- Hover over links to inspect the real destination URL
- Verify the sender domain matches the organization
- Look for unusual grammar or urgency tactics
- Avoid opening unexpected attachments
- Contact the sender through a trusted channel to confirm legitimacy
These quick checks can prevent many phishing attacks.