Understanding Spear Phishing Emails
Defining Spear Phishing
Spear phishing is a highly targeted type of phishing attack. In this method, attackers create personalized emails to deceive specific individuals or organizations into exposing sensitive information, clicking malicious links, or downloading malware.
Unlike generic phishing emails sent to large groups, spear phishing emails rely on extensive research. Attackers gather information from social media, company websites, press releases, and other public sources. These efforts allow them to include personal details such as your name, job title, recent projects, or professional connections, making the message appear authentic and convincing.
Because these emails often mimic trusted contacts like colleagues, executives, vendors, or business partners, they are significantly harder to detect than traditional phishing attempts.
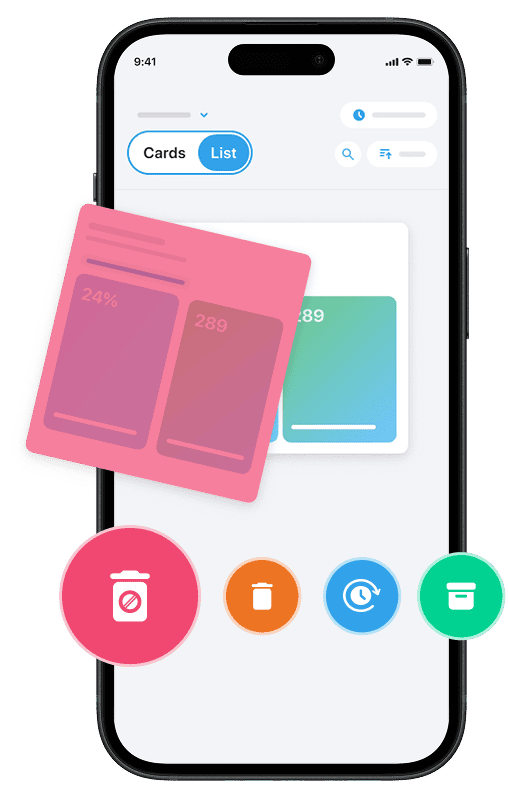
And if you want to reduce unwanted emails and better control your inbox, you can use our Cleanfox platform to clean and organize your mailbox for free.
Characteristics of Spear Phishing Emails
Spear phishing emails are carefully crafted and often include:
- Subtle email spoofing that closely resembles a colleague’s or executive’s address
- Specific references to your latest project, department, or responsibilities
- Personalized greetings instead of generic openings
- Urgent calls to action, such as transferring funds or verifying login details
- Attachments disguised as invoices, contracts, or critical updates
Common red flags may include:
- Unexpected requests for sensitive information
- Pressure tactics such as “Act now” or “Immediate action required”
- Slightly mismatched domains when hovering over links
- Requests that feel unusual or out of character for the sender
Unlike generic phishing, spear phishing emails are often grammatically correct and professionally written, making them even more dangerous. Falling for these attacks can result in credential theft, malware infections, data breaches, or full-scale business email compromise.
Real-World Examples of Spear Phishing
Case Study 1: Executive Impersonation
In 2015, employees at Ubiquiti Networks were targeted in a major spear phishing campaign. Finance staff received emails spoofing company executives, complete with look-alike domains and insider terminology. These fraudulent messages convinced employees to wire $46.7 million to overseas accounts controlled by attackers. This was a classic example of business email compromise, achieved without breaching the company’s core systems.
Similarly, in 2016, a staff member in Snapchat’s HR department responded to a spear phishing email impersonating the CEO. The attack resulted in payroll data for more than 700 current and former employees being exposed. Even major tech companies are not immune to highly targeted email attacks.
Case Study 2: Vendor and CEO Fraud
In 2016, Crelan Bank suffered a serious spear phishing attack after a high-ranking executive’s business email account was compromised. Attackers used the account to send urgent transfer requests, leading to losses of approximately $75 million. The fraud was only discovered during an internal audit.
That same year, FACC, an Austrian aerospace firm, experienced a similar attack. Spear phishers posed as the CEO and persuaded staff to approve a €50 million wire transfer. The financial impact was severe and led to executive dismissals. These incidents demonstrate how spear phishing emails can escalate into large-scale financial fraud.
How to Prevent Spear Phishing Attacks
Say goodbye to spam, clutter, and chaos.
Our smart email cleaner filters out junk, organizes your inbox, and helps you focus on what really matters.
✅ Block spam automatically
✅ Organize emails by priority
✅ Keep your inbox clean
✅ Clean old emails you don’t read
📱 Available on the App Store and Google Play.
Strengthening Email Security
Organizations should enforce DMARC with a “reject” policy, alongside SPF and DKIM, to reduce the risk of domain spoofing. Advanced email security solutions that scan and sandbox suspicious links and attachments can further prevent malicious content from reaching inboxes.
Implementing phishing-resistant multi-factor authentication methods such as FIDO2 or WebAuthn significantly reduces the risk of credential theft. Monitoring network activity for unusual behavior and deploying data loss prevention tools can also limit the damage if an account becomes compromised.
Employee Education and Awareness
Regular security awareness training is essential to help employees recognize targeted email attacks. Training should focus on identifying subtle warning signs, such as mismatched URLs, unusual tone shifts, or urgent financial requests.
Phishing simulation exercises tailored to different roles can strengthen organizational defenses. Encouraging employees to verify unusual requests through secondary channels, such as a direct phone call, adds an additional layer of protection.
Creating a culture where suspicious emails are quickly reported without hesitation significantly reduces the success rate of spear phishing campaigns.
Incident Response and Recovery
If a spear phishing email bypasses defenses, immediate action is critical. Organizations should isolate affected devices, suspend compromised accounts, revoke active sessions, and remove malicious emails across the network.
All credentials should be reset, and endpoints should be reimaged if malware is detected. Updating security controls and threat intelligence systems after an incident helps prevent similar attacks in the future. A well-documented incident response plan ensures faster containment and recovery.
Conclusion
Spear phishing emails exploit human trust through personalization, social engineering, and urgency. By using detailed reconnaissance and impersonation tactics, attackers increase the likelihood of stealing credentials, deploying malware, or triggering financial fraud.
Strong defenses include implementing DMARC, SPF, and DKIM, enforcing phishing-resistant multi-factor authentication, deploying advanced email filtering solutions, and maintaining continuous security awareness training.
One single click can cost millions. One verification step can prevent it. Always verify unexpected requests, especially those involving sensitive data or financial transactions.
FAQ
What are the key red flags that distinguish a spear phishing email from a legitimate message?
Common warning signs include:
- Slightly misspelled or spoofed sender addresses
- Unexpected urgency or pressure to act quickly
- Requests for sensitive information or financial transfers
- Mismatched URLs when hovering over links
- Attachments you were not expecting
Even well-written and professional emails can be malicious if the request is unusual or inconsistent with normal business practices.
How do cybercriminals gather the personal information used in spear phishing emails?
Attackers collect information from publicly available sources such as social media profiles, company websites, press releases, and data breaches. They may also use social engineering tactics such as pretexting or impersonation to gather additional details.
This research allows them to craft highly personalized emails that increase credibility and improve the chances of success.
What should I do if I click a malicious link or download a suspicious attachment?
If you suspect a compromise:
- Disconnect from the internet immediately
- Report the incident to your IT or security team
- Change passwords if credentials were entered
- Monitor accounts for unusual activity
Quick action can significantly reduce the impact of a spear phishing attack.
Why are spear phishing attacks particularly effective against executives?
Spear phishing attacks often target executives because of their privileged access, decision-making authority, and busy schedules. Personalized and urgent requests may bypass scrutiny, especially when attackers impersonate trusted contacts or internal leaders.
This combination of access and urgency makes executive-targeted spear phishing campaigns particularly damaging.